What Can You Do With Someone’s IP Address: Understanding the Risks and Realities
In the digital age, understanding the implications of your online footprint is crucial. One fundamental aspect of this footprint is your Internet Protocol (IP) address. This unique identifier, assigned to your device by your Internet Service Provider (ISP), acts as your digital return address. But what can you do with someone’s IP address, and what are the potential risks associated with its exposure? This article delves into the realities of IP address usage, separating fact from fiction and providing a clear understanding of its capabilities and limitations. We will explore the spectrum of actions that can be taken with an IP address, from benign geolocation to more concerning cybersecurity threats. Protecting your IP address is a key component of online safety and security.
Understanding IP Addresses: A Primer
Before exploring the potential uses of an IP address, it’s essential to understand what it is and how it functions. An IP address is a numerical label assigned to each device connected to a computer network that uses the Internet Protocol for communication. It’s analogous to a street address, allowing data to be routed to the correct destination. There are two main types of IP addresses: IPv4 and IPv6. IPv4 addresses are 32-bit numerical addresses, while IPv6 addresses are 128-bit and offer a significantly larger address space, designed to address the limitations of IPv4.
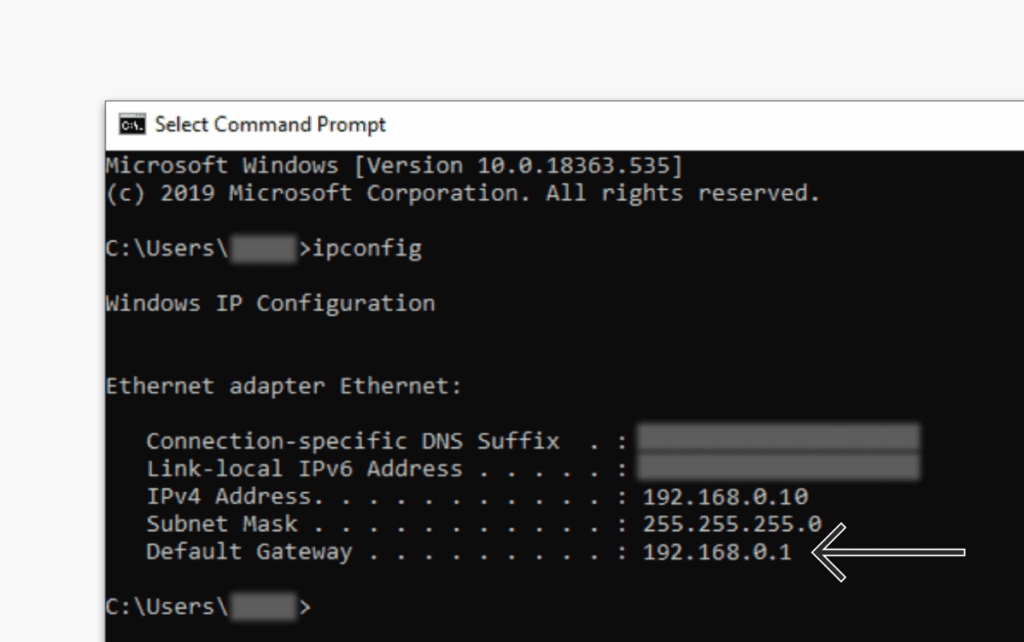
When you connect to the internet, your ISP assigns you an IP address. This address can be static (unchanging) or dynamic (changing periodically). Most residential users have dynamic IP addresses, while businesses often opt for static addresses for server stability and easier remote access. Understanding whether you have a static or dynamic IP address is relevant when considering security measures.
Geolocation: Pinpointing Location
One of the most common uses of an IP address is geolocation. By looking up an IP address in a geolocation database, it’s possible to determine the approximate geographic location of the device. This information is not precise, typically only pinpointing the city or region. The accuracy depends on the database and the ISP’s routing policies. While not precise enough to pinpoint an exact home address, it can provide a general area. For instance, knowing what you can do with someone’s IP address in terms of geolocation allows websites to customize content based on the user’s region, such as language preferences or local news.
Geolocation data is also used for targeted advertising. By knowing the general location of a user, advertisers can display ads relevant to their area, such as local businesses or events. While this can be convenient, it also raises privacy concerns as it involves tracking users’ approximate locations.
Identifying the Internet Service Provider (ISP)
An IP address can also reveal the ISP being used. This information is publicly available through WHOIS databases and other online tools. Knowing the ISP can be useful for troubleshooting network issues or identifying potential sources of spam or malicious activity. For example, if you receive a suspicious email from a particular IP address, you can identify the ISP and report the activity to them. This is a relatively harmless aspect of what you can do with someone’s IP address.
Tracking Online Activity (Limited)
While an IP address can be used to track online activity, it’s important to understand its limitations. An IP address alone cannot directly identify an individual. It identifies the device or network being used. However, when combined with other information, such as browsing history, cookies, and account logins, it can be used to build a profile of a user’s online behavior. This is where privacy concerns become more significant. Websites and online services often use IP addresses in conjunction with other tracking technologies to personalize content, target advertising, and analyze user behavior.
It is important to note that VPNs and proxy servers can mask your real IP address, making it more difficult to track your online activity. When you use a VPN, your internet traffic is routed through a server in a different location, effectively hiding your original IP address. This is a common practice for individuals who want to protect their privacy and anonymity online.
Potential for Cyberattacks and Hacking
One of the more concerning aspects of what you can do with someone’s IP address is the potential for cyberattacks. While an IP address alone cannot be used to hack into a device, it can be used as a starting point for various attacks. For example, an attacker can use an IP address to scan for open ports and vulnerabilities on a device. If vulnerabilities are found, the attacker can exploit them to gain unauthorized access.
Denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks are also common threats. In a DoS attack, an attacker floods a target device or network with traffic, making it unavailable to legitimate users. In a DDoS attack, the traffic comes from multiple sources, making it more difficult to mitigate. These attacks can be launched using an IP address as the target. While knowing what you can do with someone’s IP address, it’s also important to take steps to protect yourself from such attacks.
Furthermore, an attacker may attempt to use social engineering tactics to gather more information about the target, using the IP address as a starting point. For instance, they might contact the ISP and impersonate the account holder to gain access to sensitive information. This highlights the importance of protecting your personal information and being wary of suspicious requests.
Legal and Ethical Considerations
The use of IP addresses raises various legal and ethical considerations. While it is generally legal to look up an IP address and determine its geolocation or ISP, using this information for malicious purposes, such as hacking or launching cyberattacks, is illegal. Privacy laws, such as GDPR and CCPA, also regulate the collection and use of IP addresses and other personal data.
Ethically, it is important to respect individuals’ privacy and avoid using IP addresses to track or monitor their online activity without their consent. Transparency and accountability are crucial when collecting and using IP address data. Websites and online services should clearly disclose their practices and provide users with control over their data.
How to Protect Your IP Address
Given the potential risks associated with exposing your IP address, it’s important to take steps to protect it. Here are some common methods:
- Use a VPN: A VPN encrypts your internet traffic and routes it through a server in a different location, effectively hiding your real IP address. [See also: Best VPN Services for Privacy]
- Use a Proxy Server: Similar to a VPN, a proxy server acts as an intermediary between your device and the internet, masking your IP address.
- Use Tor: Tor is a free and open-source software that anonymizes your internet traffic by routing it through a network of relays.
- Be Careful What You Share Online: Avoid sharing your IP address or other personal information on public forums or social media platforms.
- Use a Firewall: A firewall can help protect your device from unauthorized access and prevent attackers from scanning your IP address for vulnerabilities.
Debunking Myths About IP Addresses
There are several common misconceptions about IP addresses that need to be addressed. One myth is that an IP address can be used to directly identify an individual. As mentioned earlier, an IP address identifies the device or network being used, not the individual. Another myth is that changing your IP address will completely protect you from online tracking. While it can make it more difficult to track you, it is not a foolproof solution. Websites and online services can still use other tracking technologies, such as cookies and browser fingerprinting, to identify you.
The Future of IP Addresses
The future of IP addresses is likely to be shaped by the ongoing transition from IPv4 to IPv6, as well as advancements in privacy-enhancing technologies. IPv6 offers a significantly larger address space, which will help address the limitations of IPv4 and support the growing number of internet-connected devices. Privacy-enhancing technologies, such as differential privacy and homomorphic encryption, are also being developed to protect users’ data while still allowing it to be used for analysis and other purposes. These are important considerations when thinking about what you can do with someone’s IP address in the future.
Conclusion: Understanding the Power and Limitations
Understanding what you can do with someone’s IP address is crucial for protecting your online privacy and security. While an IP address alone cannot be used to directly identify you or hack into your device, it can be used as a starting point for various attacks and tracking activities. By taking steps to protect your IP address and being aware of the potential risks, you can significantly reduce your exposure to online threats. Staying informed about the latest privacy-enhancing technologies and best practices is also essential in the ever-evolving digital landscape. Remember that responsible use of IP address information is vital for maintaining a safe and secure online environment.
